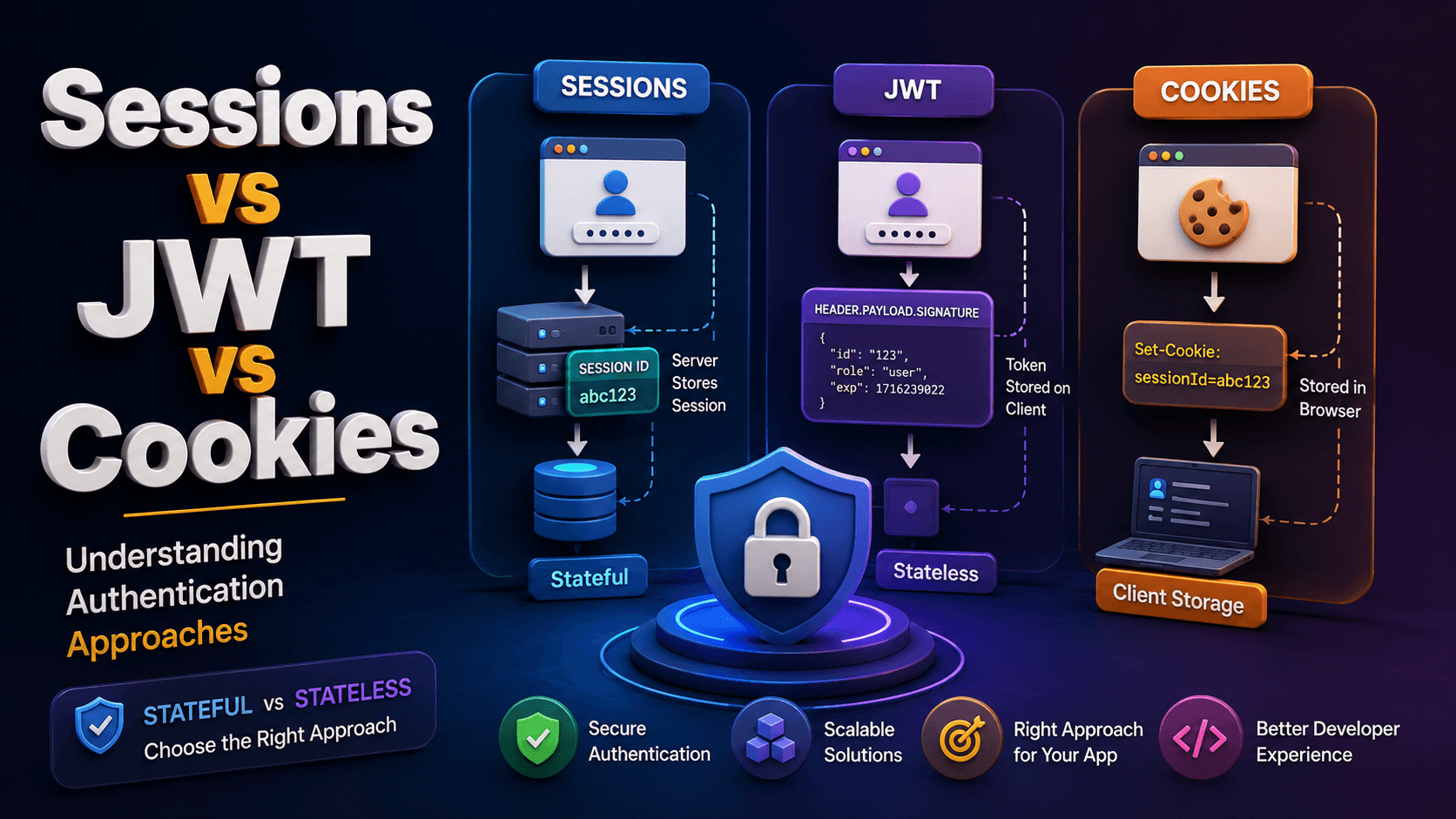
Sessions vs JWT vs Cookies: Understanding Authentication Approaches
Authentication is one of the most important parts of backend development.
Whenever users log in to an application, the server needs a way to identify them in future requests.
This is where concepts like:
Sessions
Cookies
JWT (JSON Web Tokens)
come into play.
Many beginners confuse these terms because they are often used together.
In reality, they solve different parts of the authentication process.
In this article, we’ll understand how sessions, cookies, and JWTs work, the difference between stateful and stateless authentication, and when each approach should be used in real-world applications.
Why Authentication is Needed
Imagine a user logs into a website.
After login, every future request should identify:
who the user is
whether they are authenticated
what permissions they have
But HTTP is stateless by default.
That means every request is treated as completely new.
Authentication systems solve this problem by storing or sending user identity information between requests.
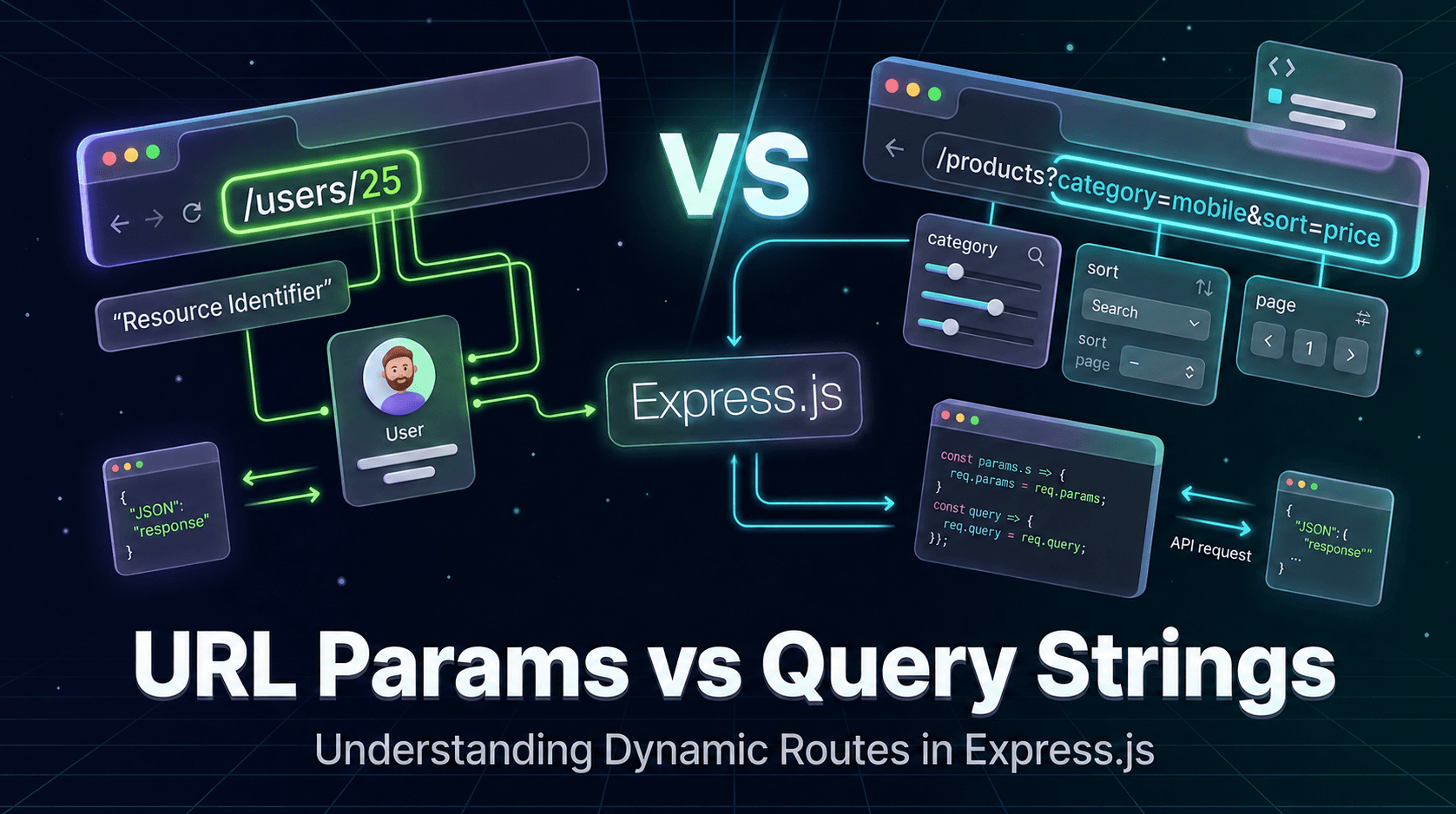
What are Cookies?
Cookies are small pieces of data stored in the browser.
The server sends cookies to the client, and the browser automatically sends them back with future requests.
Example response header:
Set-Cookie: sessionId=abc123
The browser stores it and sends it automatically:
Cookie: sessionId=abc123
Cookies themselves are not authentication systems.
They are simply a storage mechanism used to store:
session IDs
JWT tokens
user preferences
tracking information
What are Sessions?
A session is a server-side authentication mechanism.
In session-based authentication:
User logs in
Server creates a session
Session data is stored on the server
A session ID is sent to the browser through cookies
Browser sends the session ID with every request
Server verifies the session
Session Authentication Flow
User Login
↓
Server Creates Session
↓
Session Stored in Database/Memory
↓
Session ID Sent in Cookie
↓
Browser Stores Cookie
↓
Browser Sends Cookie in Future Requests
↓
Server Verifies Session
Example of Session-Based Authentication
After login :
req.session.user = {
id: user._id,
email: user.email
};
The server stores this session data.
The client only stores the session ID.
What are JWT Tokens?
JWT stands for JSON Web Token.
A JWT is a self-contained token that stores user information directly inside the token itself.
Unlike sessions, JWT authentication usually does not require storing session data on the server.
Example JWT structure:
HEADER.PAYLOAD.SIGNATURE
Example payload:
{
"id": "123",
"email": "user@example.com"
}
The token is signed by the server to prevent tampering.
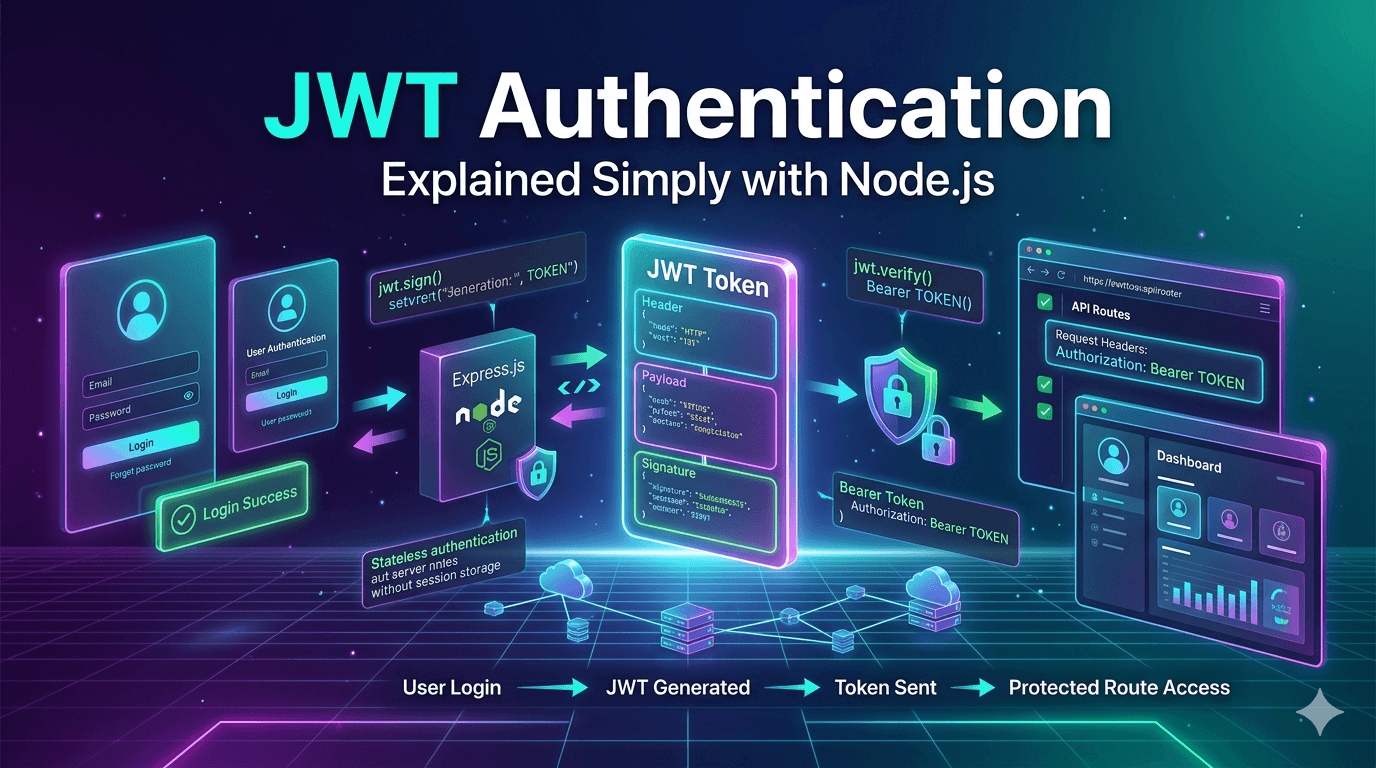
JWT Authentication Flow
User Login
↓
Server Creates JWT
↓
JWT Sent to Client
↓
Client Stores Token
↓
Client Sends JWT in Requests
↓
Server Verifies JWT Signature
↓
Request Authorized
Example JWT Authentication
Generating token:
const token = jwt.sign(
{
id: user._id
},
process.env.JWT_SECRET,
{
expiresIn: "7d"
}
);
Sending token:
res.json({
token
});
Client sends token in headers:
Authorization: Bearer jwt_token_here
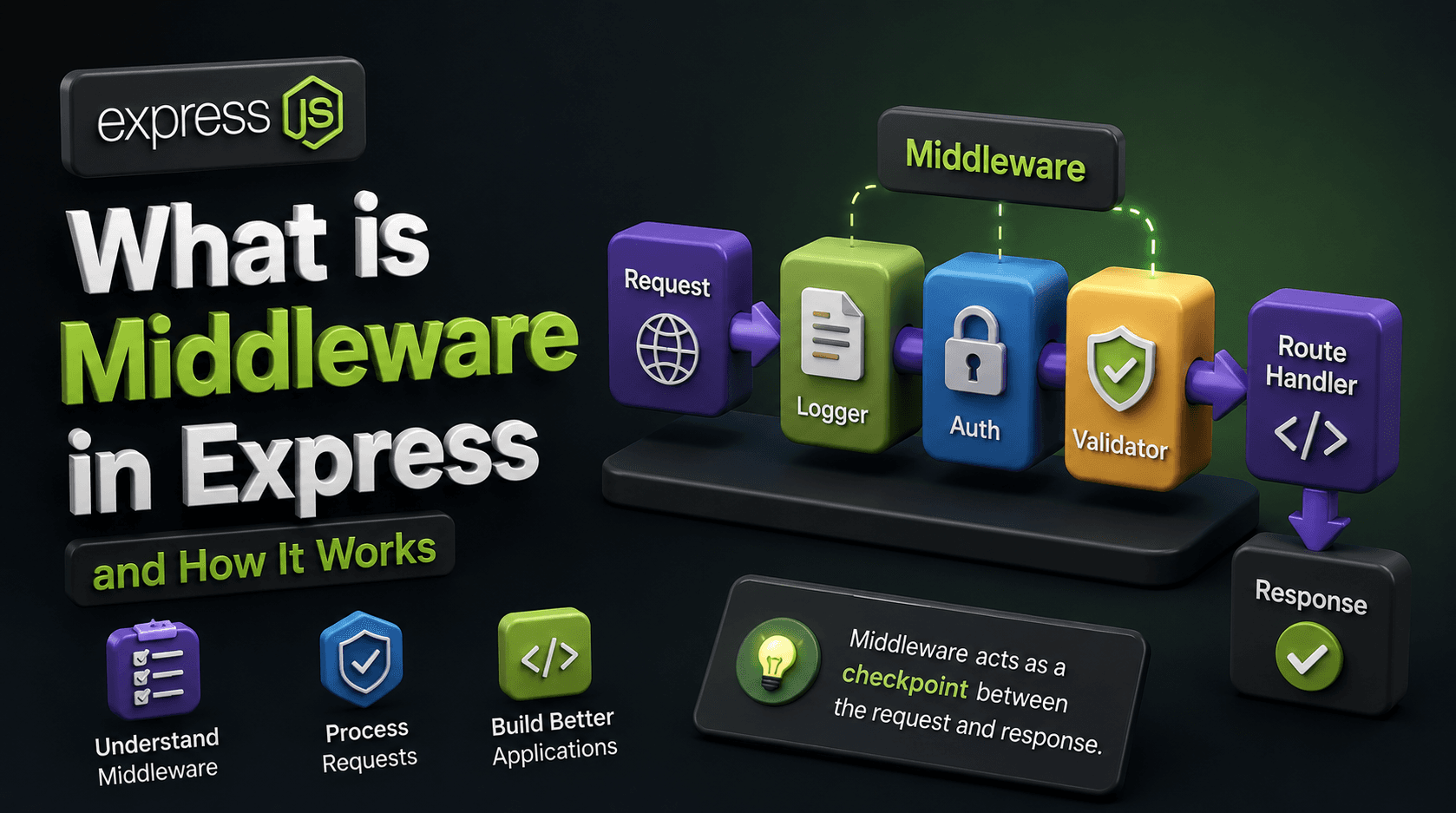
Stateful vs Stateless Authentication
This is the biggest conceptual difference.
Stateful Authentication
Sessions are stateful.
The server stores authentication data.
Example:
Server Memory / Database
↓
Session Data Stored
The server must remember every logged-in user.
Stateless Authentication
JWT is stateless.
The server does not store user login state.
The token itself contains the required information.
Example:
Client Holds Token
↓
Server Only Verifies Signature
This makes JWT systems easier to scale.
Sessions vs JWT Authentication
Here’s the core difference.
| Feature | Sessions | JWT |
|---|---|---|
| Storage | Server-side | Client-side |
| Authentication Type | Stateful | Stateless |
| Scalability | Harder at large scale | Easier to scale |
| Token Size | Small session ID | Larger token |
| Server Memory Usage | Higher | Lower |
| Logout Handling | Easy | Slightly harder |
| Token Revocation | Easy | More complex |
| Automatic Browser Support | Yes via cookies | Usually manual |
| Mobile/API Friendly | Less ideal | Excellent |
| Best For | Traditional web apps | APIs & modern apps |
How Cookies Work with Sessions
Sessions usually depend on cookies.
Example:
Cookie:
sessionId=abc123
The cookie stores only the session ID.
The actual user data remains on the server.
How Cookies Work with JWT
JWTs can also be stored inside cookies.
Example :
Cookie:
token=jwt_token_here
Or stored in:
localStorage
sessionStorage
memory
When to Use What
Session-Based Authentication
Sessions are great for:
traditional server-rendered websites
admin panels
applications with tight server control
systems requiring easy logout handling
Examples:
banking portals
dashboards
CMS systems
Advantages:
easy invalidation
secure server-controlled sessions
simpler browser integration
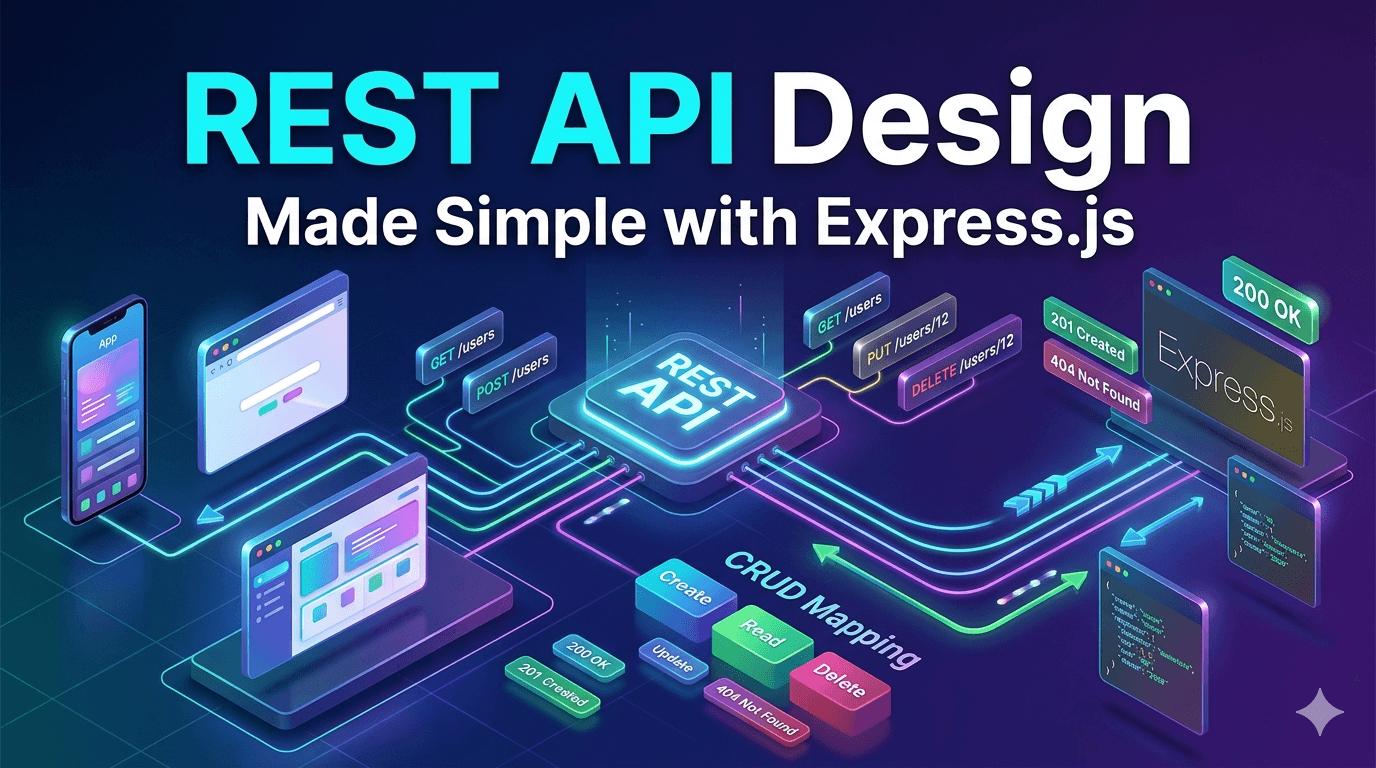
JWT Authentication
JWT works best for:
REST APIs
mobile apps
microservices
distributed systems
frontend-backend separated architectures
Examples:
React frontend + Node backend
mobile applications
third-party API authentication
Advantages:
scalable
lightweight server load
cross-platform friendly
Conclusion
Sessions, cookies, and JWTs are all important parts of authentication systems, but they serve different purposes.
Cookies are browser storage mechanisms
Sessions store authentication state on the server
JWT stores authentication data inside signed tokens
The biggest difference comes down to:
stateful authentication (sessions)
stateless authentication (JWT)
Neither approach is universally better.
Choosing the right authentication method depends on your application architecture, scalability needs, and development style.
Understanding these concepts clearly is essential for building secure and scalable backend applications.